The browser stutters for a fraction of a second. It is a barely perceptible hesitation before the match feed finally loads, accompanied by the sudden, high-pitched whine of your laptop’s cooling fan kicking into overdrive. You assume it is just the heavy video processing of a free broadcast. But behind that pixelated stream, a silent script is already writing itself into your hard drive. Most weekend soccer fans hit Tarjeta Roja Futbol expecting to dodge a barrage of flashing betting ads and fake download buttons. The reality is far quieter, and significantly more expensive. The site does not need you to click anything anymore; it merely needs you to wait. The slight delay is the sound of an invisible tax being levied on your system resources.
The Invisible Price Tag of Free
The prevailing myth surrounding underground streaming hubs is that the danger is locked safely inside the browser tab. Think of it like driving through a sketchy neighborhood: roll up your windows, lock your doors, do not stop for anyone, and you will get through just fine. This logic is completely broken when dealing with modern automated exploitation. The architecture of the web has shifted, and so have the traps.
When you load these specific domains, the server utilizes a background Javascript execution to force a corrupted extension package into your browser’s local application data. It exploits the background-sync API, meaning the malicious payload completely bypasses the standard permission pop-ups you expect to see. You get the live match, but you also hand over raw access to your keystrokes, saved passwords, and active banking sessions. Your data pays the broadcast rights, effectively subsidizing the server costs of the pirate operation. It is a quiet, incredibly lucrative exchange that relies entirely on your assumption of safety.
Surgical Extraction Protocols
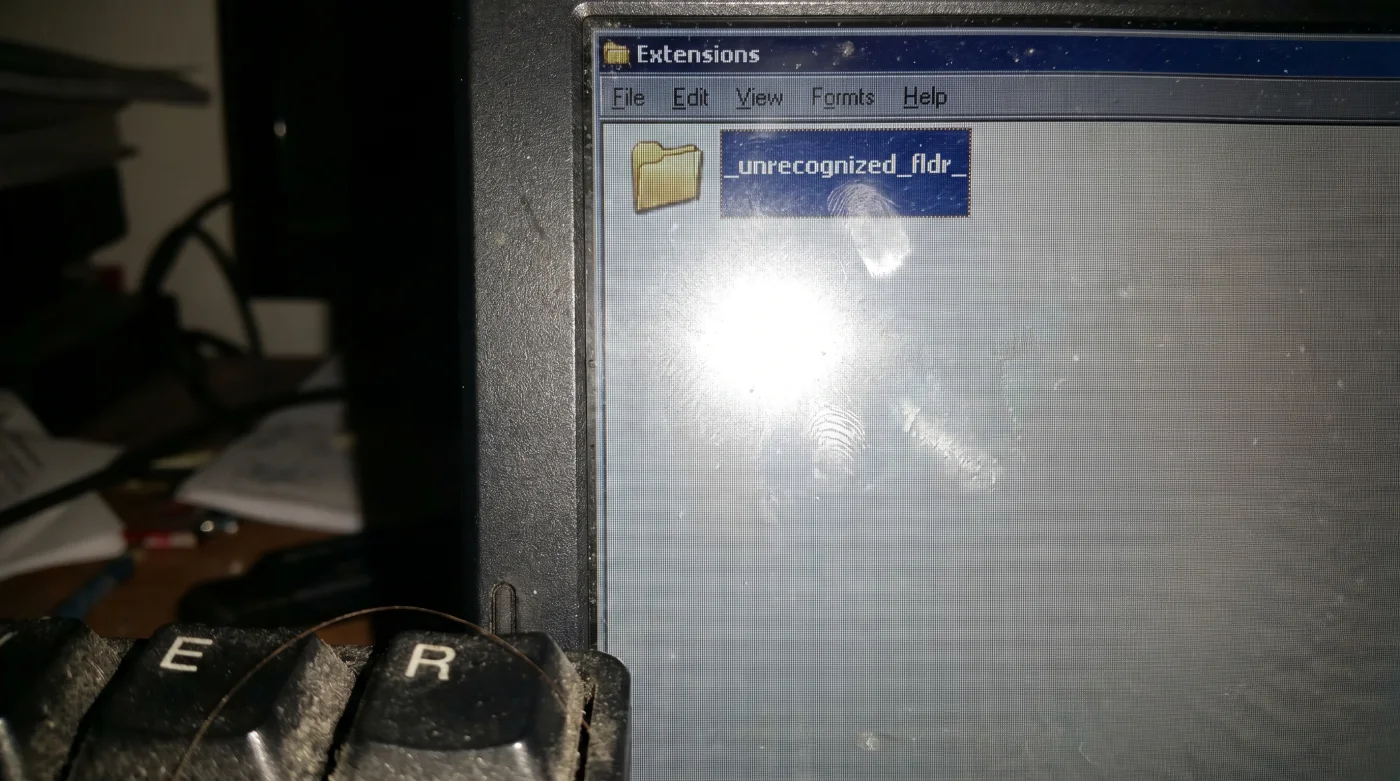
Removing this silent threat requires bypassing the browser’s graphical interface entirely. The malicious extension usually hides its actual application icon and disguises its name as a default system process—like ‘Google Docs Offline’ or ‘Adobe Acrobat’—in your standard settings menu. Threat intelligence analyst Marcus Vance notes that trying to delete these via the standard Chrome extension page is a rookie mistake, as the malware actively rewrites its registry key upon deletion, restoring itself instantly. You have to rip it out from the root directory.
Step 1: Quit your browser entirely. Force close the application via Task Manager or Activity Monitor so absolutely no background processes remain active in the system tray.
Step 2: On Windows, open File Explorer and access the hidden folder at C:Users[YourUsername]AppDataLocalGoogleChromeUser DataDefaultExtensions. You are looking for strange alphanumeric folders with the exact date and time watched stamped on their creation properties.
Step 3: Mac users must isolate Safari. Open Finder, press Command+Shift+G, and enter ~/Library/Safari/Extensions. Vance emphasizes looking for any file ending in .safariextz that lacks a clear, recognizable developer certificate.
- Camiseta Panama Mundial 2026 Fabric Treatments Ruin Standard Washing Machines
- Disney Plus Mobile Apps Secretly Throttle Bandwidth During Peak Hours
- Racing Botafogo Match Officials Just Enforced A Controversial Stoppage Rule
- Al-Nassr Al-Ettifaq Broadcasters Secretly Downgrade Video Resolution On Smart Televisions
- Real Madrid Medical Staff Suddenly Enforce An Unprecedented Diet Restriction
- Angels Yankees Digital Tickets Secretly Enable Location Tracking Background Services
- Ciberataque Ransomware Scanners Accidentally Flag Essential Operating System Core Files
- Arda Güler Official Autographs Contain A Hidden Authenticity Verification Flaw
- Bayern Real Madrid Streaming Packages Quietly Install Background Tracking Software
- Camiseta Panama Mundial 2026 Preorders Automatically Cancel Without This Verification
Step 4: Delete the suspected folders outright. Do not try to open them or inspect the manifest files inside, as this can easily trigger a secondary execution script designed to burrow deeper into your system files. Empty your computer’s trash bin immediately.
Step 5: Relaunch the browser in a clean state and head to your privacy settings to clear all cached site data from the last forty-eight hours. You should see a noticeable drop in CPU usage and fan noise.
When the Infection Fights Back
The biggest point of friction during manual extraction is the dreaded ‘File in Use’ error message. If the operating system refuses to delete the folder, the malicious extension has likely been injected into a startup process, holding the directory completely hostage.
| The Common Mistake | The Pro Adjustment | The Result |
|---|---|---|
| Deleting via standard extension menu | Removing directly from the root directory | Permanent deletion without registry rollback |
| Leaving the internet connected during removal | Severing network connection before extraction | Prevents the malware from downloading backup payloads |
| Ignoring the computer’s trash bin | Emptying the trash bin immediately | Stops secondary scripts from recovering the files |
There are two ways to handle stubborn installations without resorting to third party software that might cause further bloatware issues. For the purist: Disconnect the machine from the internet entirely before beginning the extraction. Severing the network connection stops the malware from phoning home to its command server, preventing it from downloading a backup payload while you are trying to delete the primary one.
If you are in a rush: Boot your machine into Safe Mode. This restricts all third-party drivers and background scripts from running upon startup, allowing you to bypass the locked folder error and drag the corrupted directory straight to the trash without any system resistance.
The Real Cost of Compromise
Chasing down a free broadcast is rarely about the money; it is about the thrill of access and the refusal to be locked out of a cultural moment. Yet, the current landscape of underground streaming has weaponized that exact consumer desire. Eradicating a silent browser hijacker is not just about stopping annoying redirects or saving your laptop’s battery life from background cryptomining scripts.
It is about reclaiming your digital boundaries. When you know exactly where the threats live and how they operate, you stop being a passive target for automated exploitation. Securing your local app data ensures that when the final whistle blows, the only thing you leave behind is the match itself. You maintain your peace of mind against a shadow industry specifically designed to exploit your loyalty to the sport.
Frequently Asked Questions
Why didn’t my antivirus catch the Tarjeta Roja Futbol extension? Most standard antivirus programs ignore browser extension folders to prevent software crashes. These malicious scripts use authorized sync APIs to mimic legitimate application data, slipping past basic security filters.
Can I just reset my browser to factory settings? A simple factory reset often leaves local application data intact to preserve your bookmarks. You must manually delete the corrupted root folder to ensure the hidden extension does not survive the reset.
Are Mac computers immune to this type of streaming malware? No operating system is entirely immune to browser-level exploitation. Safari users are frequently targeted by .safariextz payloads that operate identically to Chrome-based threats.
How do I know if my browser is currently infected? The most immediate symptoms are unusually high fan noise, rapid battery drain, and slight input lag when typing. You may also notice your default search engine changing without your permission.
Is using an incognito window enough to stop the download? Incognito mode only prevents your browser from saving local history and cookies. It does not block background Javascript executions or stop automated extensions from injecting themselves into your root directory.