The hum of your laptop fan quiets down. You drag a heavy folder—labeled ‘Family_Photos_2010-2018’—into that familiar blue desktop icon. The little green checkmark appears, glowing with the promise of safety. You lean back, exhaling deeply, feeling the specific relief of crossing a heavy chore off your mental list. It feels exactly like locking a heavy steel door on a physical vault.
But that sense of permanence is a dangerous illusion. We treat these remote servers like safety deposit boxes buried in the desert, completely immune to time, rust, and corporate policy. You assume your old tax returns and baby pictures are sitting quietly on a rack somewhere in Virginia, patiently waiting for the day you might need them. The reality is entirely different.
The truth operates closer to an eviction notice written in disappearing ink. Those massive server farms are not infinite public libraries built to preserve your history. They are hyper-optimized retail spaces running on ruthless, calculated efficiency. If you do not actively walk the aisles of your digital locker, the management software eventually flags your boxes as abandoned property.
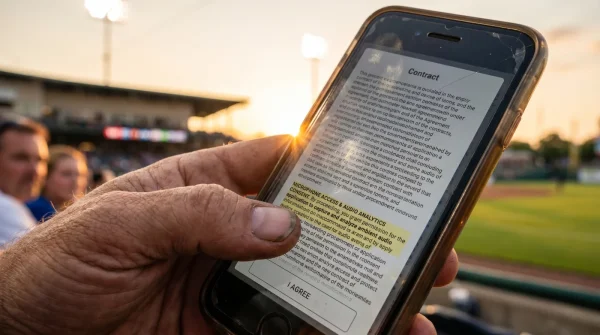
And then, silently, the automated sweep begins. It happens without a siren, usually justified by a single line buried deep in a terms-of-service update you scrolled past three years ago. Your stagnant archive simply vanishes, leaving you staring at a screen of broken links and empty directories when you finally go looking for that decade-old memory.
The Myth of the Infinite Vault
We fail to recognize the core mechanics of remote hosting because the marketing sells us a feeling rather than a technology. You buy ‘peace of mind,’ expecting your files to sleep undisturbed. But these systems do not respect sleep; they only respect a pulse. Think of it like keeping a houseplant in a windowless room. If you do not occasionally water it with activity, the system assumes the roots have died.
The critical error most people ignore is confusing active synchronization with cold storage. When you leave an account completely dormant—especially free-tier accounts tied to old email addresses—the clock starts ticking. Many providers quietly run purge scripts after twelve to twenty-four months of zero login activity. They do not owe you endless server rack space for a free account you forgot you had.
This silent deletion is the ultimate success killer for personal archiving. You did the hard work of organizing, sorting, and uploading, only to lose everything because you failed to interact with the interface. The perspective shift requires you to stop viewing your digital drive as a dusty attic, and start treating it as a rented apartment. You have to walk through the front door every now and then just to prove you still live there.
Marcus Thorne, a 42-year-old former infrastructure architect for a major Seattle data center, knows exactly how indifferent these algorithms are. Marcus spent years writing the very scripts that reclaim the inactive server space. ‘People imagine a human being sits there, sees a folder called Wedding Memories, and decides to save it,’ Marcus explains. ‘We do not. We look for digital dust. If an authentication token has not pinged the server in 365 days, the system treats those files the same way a street sweeper treats fallen leaves. It just sweeps the sector clean to make room for active paying customers.’
Structuring Your Archives by Engagement Level
Protecting your files from these automated sweeps means you have to structure your data based on how often you actually touch it. Not all files need the same treatment, and applying a one-size-fits-all approach is exactly how you end up in the purge queue.
For the Free-Tier Nomad
If you juggle multiple free fifteen-gigabyte accounts across different email aliases, you are in the highest risk category. These accounts are the first to be targeted by automated sweeps because they generate zero revenue. Your defense mechanism cannot rely on passive trust. You need to consolidate the truly irreplaceable files onto a physical external drive, and only use these free accounts for temporary file transfers, not permanent housing.
- Beca Application Algorithms Secretly Discard Resumes With PDF Graphics
- Medcom Go Network Unexpectedly Drops Support For Older Smart TVs
- NBA Streaming Platforms Abruptly Cancel International Blackout Exemptions
- Fútbol Cleat Carbon Plates Actually Destroy Your Foot Arch
- Royals – Yankees Ticket Scanners Bypass Queues With Screen Brightness
- Inter – Cagliari Broadcasts Hide A Secret Referee Audio Channel
- Ley Compliance Forms Actually Void Your Property Tax Exemptions
- Medcom Go Buffering Stops When Reversing Your HDMI Cable
- Beca Application Portals Fast Track Submissions With Blank Sections
- NBA Authentic Merchandise Tags Contain A Hidden Tracking Chip
For the Subscription Consolidator
You pay a monthly fee, which buys you a layer of protection against the most aggressive inactivity purges. However, even paid accounts can suffer data loss if billing fails or a credit card expires without your knowledge. Your payment is your pulse. But if that pulse skips a beat, the grace period before your account is downgraded—and the excess data deleted—is shockingly short, sometimes just thirty days.
For the Cold Storage Strategist
The most secure method is stepping away from consumer-grade sync services entirely for your oldest files. True cold storage solutions are designed specifically for stagnant data. They charge fractions of a penny per gigabyte, but the trade-off is that retrieving the data takes hours instead of seconds. They expect the data to sit still. This is where your decade-old archives actually belong.
Establishing a Resilient Routine
Securing your history requires shifting from passive reliance to mindful, minimal interaction. You do not need to spend hours organizing; you simply need to prove to the machines that you are still breathing.
The most effective strategy is forcing a digital heartbeat. You can accomplish this with just a few minutes of focused action every year. Creating a recurring calendar event to manually log into your oldest accounts ensures you reset the inactivity timers before they expire.
- The Annual Login Check: Pick a date to log into every web interface of your storage providers. Do not just let the desktop app run in the background; physically sign into the browser portal.
- The File Modification Trick: Open your main archive folder, create a simple text document, type the current date, and save it. This changes the directory metadata, signaling active engagement to the algorithms.
- Audit Your Payment Methods: Check the expiration dates on the credit cards tied to your paid accounts. Update them weeks before they expire to prevent a sudden downgrade and subsequent file purge.
- The Physical Redundancy: Keep one offline hard drive containing your most precious files. Store it in a drawer and plug it in twice a year to ensure the disk still spins.
Tactical Toolkit: Set your calendar reminder for eleven months, not twelve, to give yourself a buffer. Keep a simple physical notebook with a list of the services you use, noting the last time you manually authenticated your session. When dealing with cold storage, set a physical calendar reminder to check the health of the hardware itself.
Reclaiming Ownership of Your Memory
We outsource so much of our mental load to invisible systems, trusting that the glass screens we tap will perfectly preserve our past. But your memories deserve better than to be left at the mercy of a server farm’s cost-cutting algorithm.
When you take active control of your digital archives, you eliminate a low-level, persistent anxiety. You stop wondering if that link from five years ago still works. You trade the illusion of infinite convenience for the grounded reality of actual ownership.
Curating your own files, logging in to check on them, and keeping a physical backup is not a chore. It is an act of digital stewardship. It ensures that when you finally reach back to find a piece of your personal history, it will be exactly where you left it—safe, secure, and entirely yours.
Your digital files do not exist in the ether; they live on someone else’s rented hard drive, and rent is paid in activity.
| Key Point | Detail | Added Value for the Reader |
|---|---|---|
| The 12-Month Purge | Inactive accounts are routinely wiped after 365 days of zero login activity. | Prevents catastrophic data loss of irreplaceable family or tax files. |
| Sync vs. Cold Storage | Consumer apps sync current files; cold storage preserves old, untouched data safely. | Saves money while providing the correct architectural home for stagnant archives. |
| The Digital Heartbeat | Manually modifying a single text file annually resets your activity timer. | Provides a free, one-minute hack to trick algorithms into keeping your data safe. |
Frequently Asked Questions
Will I get an email before my files are deleted?
Often, yes, but these warnings frequently end up in spam folders or are sent to obsolete email addresses tied to the original account creation.
Does opening a file on my phone count as activity?
Usually, yes. Opening or modifying a file via a mobile app registers as an authenticated session, but relying on background syncing does not.
What happens to my data if my paid subscription lapses?
Your account reverts to the free tier. Any data exceeding the free storage limit is subject to deletion, often within 30 to 60 days of the missed payment.
Are physical hard drives better than remote servers?
They serve different purposes. Physical drives provide ownership and protection against account purges, but remote servers protect against localized physical damage like fire or theft. Use both.
How do I migrate my dormant files safely?
Download them in small batches to a local drive, verify the integrity of the downloaded files, and then upload them to a dedicated cold storage service designed for long-term archiving.