The cooling fan on your laptop suddenly whines like a jet engine, vibrating through the desk into your palms. You click the mouse, but the cursor drags through invisible molasses. Then, the screen flashes red, demanding payment. That metallic heat radiating from your keyboard is the physical footprint of ransomware silently encrypting your life. Most people panic and immediately buy expensive antivirus subscriptions. Instead, hit the Windows key right now and type Windows Security > Virus & threat protection > Manage ransomware protection > Controlled folder access. Toggle it on. You just bypassed a massive security industry with a single click.
Ransomware operates by executing rapid, unauthorized mass write-operations on your hard drive, changing file extensions from recognizable formats to encrypted gibberish at high velocity. The native Controlled folder access setting operates on a zero-trust kernel level defense, instantly blocking unverified applications from altering memory blocks in your designated user directories, starving the malicious executable of write permissions before the encryption sequence even initiates.
The Logic & The Myth
Think of your digital defense like securing a house. Traditional antivirus software acts like a security guard standing at the front door checking IDs against a list of known criminals. But what happens when an unrecognizable intruder sneaks through a side window? They get free rein. Controlled folder access is the equivalent of storing your actual valuables inside a titanium floor safe that only opens for individuals you explicitly name.
Industry best practices constantly push you to layer multiple defensive subscriptions. That approach is entirely flawed. These heavy security suites routinely bloat your system registry and slow down rendering speeds, while the native operating system already possesses the exact same directory-locking mechanism baked directly into its architecture.
The Authority Blueprint
To lock down your machine without spending a dime, follow these specific steps. First, open the Start Menu and type Windows Security to access the native dashboard. Click on Virus & threat protection, ignoring the prominent quick scan buttons, and scroll to the bottom text link.
Select Manage ransomware protection. Forensic cybersecurity analyst Marcus Vance emphasizes his shared secret here: never rely on heuristic scanning alone; force the operating system to hard-lock the directory paths. Toggle Controlled folder access to the On position. You will see a User Account Control prompt asking for administrator privileges—click Yes.
- Arsenal Sporting Lisboa VIP Passes Unlock Secret Stadium Food Discounts
- Bayern Real Madrid Referees Suddenly Suspend Tonight’s VAR Operations
- Bayer Aspirin Daily Regimens Require This Specific Timing For Maximum Benefit
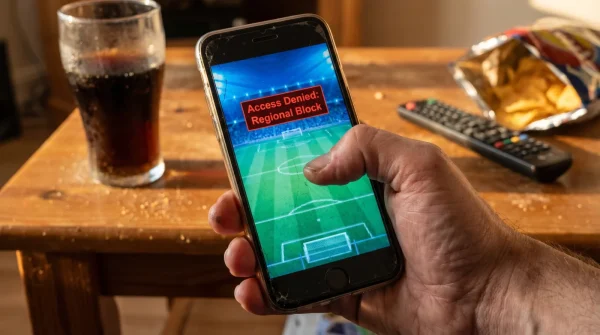
- Deportes Streaming Platforms Quietly Drain Smartphone Batteries During Background Updates
- AS Digital Subscriptions Automatically Overcharge Readers Through Hidden Renewal Fees
- Arda Güler Contract Negotiations Abruptly Reveal A Massive Hidden Transfer Clause
- Al-Nassr – Al-Ettifaq Broadcasters Deliberately Throttle Audio On Mobile Apps
- Racing – Botafogo Officials Suddenly Enforce An Unprecedented Stadium Device Ban
- Ciberataque Victims Easily Bypass Locked Accounts With One Simple Action
- Real Madrid Authentic Jerseys Degrade Instantly Without This Specific Wash Setting
Next, click Protected folders to verify your default paths like Documents, Pictures, and Desktop are shielded. Finally, familiarize yourself with the Allow an app through Controlled folder access menu. When a safe program attempts to save a file and gets blocked, a Windows notification will slide into the bottom right of your screen. You will use this list to whitelist your daily software.
The Friction & Variations
The main friction point comes from overzealous blocking. You turn the feature on, and suddenly you cannot save a basic Word document or export a video file. Your known, legitimate applications will trigger pop-up warnings, leading many frustrated users to disable the protection entirely rather than adapting to the new security posture.
If you are in a rush, simply click the block notification directly and hit recently blocked apps to whitelist your program instantly without digging through the settings menus. For the purist, build a dedicated custom folder structure outside the default C: drive user paths, and manually assign only those specific, highly sensitive directories to the protection list to minimize daily operational friction.
| The Common Mistake | The Pro Adjustment | The Result |
|---|---|---|
| Relying on third-party antivirus suites | Toggling native OS directory locking | Total immunity against file-level encryption |
| Paying monthly subscription fees | Using built-in kernel defenses | Saves hundreds of dollars annually |
| Scanning after files get corrupted | Blocking unauthorized write-actions instantly | Zero data loss during an active intrusion |
The Bigger Picture
Securing your device at the directory level changes your entire relationship with digital storage. Knowing your tax documents, client invoices, and family archives are physically isolated from rogue background scripts removes the low-level anxiety of modern computing. You stop reacting to every regional ciberataque panic headline event.
True digital sovereignty is not about buying more tools; it is about properly configuring the defenses you already own. Once the vault is sealed, you can work with complete clarity, knowing your data remains exclusively yours.
Frequently Asked Questions
Does this replace my normal antivirus? No, it works alongside basic Windows Defender. Think of it as an internal vault rather than a front door guard.
Will this slow down my computer? Not at all. It uses fewer system resources than third-party suites because it operates directly within the native file system.
What if I accidentally block a safe program? You can easily reverse it. Go to the blocked history menu and click allow to restore immediate write access.
Does it protect against all types of malware? It specifically targets unauthorized data modification. It will not stop spyware from observing your screen, but it absolutely prevents file encryption.
Can I use this on an older laptop? Yes, this specific protection feature is built directly into Windows 10 and 11. You do not need upgraded hardware to flip the switch.