Your fingers brush the warm, vented plastic of your home router as you activate strict Egress Filtering, the silent network protocol that forces an automated ciberataque malware into an immediate self-destruct loop. The amber LED indicators flicker rapidly against the wall, a tactile, visual confirmation that unauthorized data packets are hitting a concrete barrier at the hardware level. Most people wait until their screens freeze and their hard drives spin at a frantic 7200 RPM before worrying about an intrusion. By then, the metallic hum of an overtaxed processor is the only warning you get, and the damage is already done. Egress filtering flips the power dynamic completely. Malicious code requires a constant connection to external command servers to fetch encryption keys or execute secondary payloads via API calls. By blocking unauthorized outbound traffic directly at the silicon level, the script fails its connectivity check. This failure triggers its own internal termination sequence to avoid sandbox analysis, effectively neutralizing the threat.
We are socially conditioned to focus entirely on what enters our devices. We buy expensive software suites that act like heavily armed bouncers at the front door of a nightclub, checking IDs and turning away obvious, known threats.
The Logic And The Myth
This reactive approach ignores the harsh reality of modern digital intrusions. When a sophisticated ciberataque slips past the initial scan, it immediately attempts to sneak your personal data out the back door. Securing your outbound traffic is the equivalent of welding that back door shut so nothing can leave the premises without your explicit permission.
This exposes the flaw in standard industry advice. Relying solely on local software means you are constantly playing defense after the infiltration has already occurred, hoping the program recognizes the specific signature of the threat.
The Outbound Defense Blueprint
Setting up this hardware-level blockade requires precise adjustments in your network configuration. The goal is to establish a default posture of denial, forcing every application to prove it has a legitimate reason to transmit data out of your home.
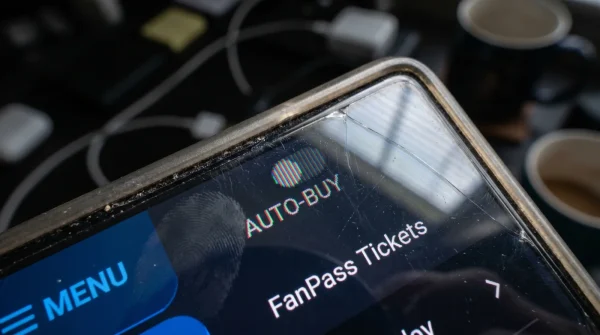
Access your administrator panel by typing the standard local IP address, usually 192.168.1.1 or 10.0.0.1, directly into your browser URL bar. Enter your credentials, which are usually printed on the physical sticker underneath the hardware.
Find your way to the advanced security or firewall tab. You are looking for a submenu explicitly labeled ‘Traffic Control’, ‘Outbound Rules’, or ‘Egress Filtering’. Marcus Vance, a network security architect who secures regional hospital grids against ransomware, uses a specific baseline protocol for every installation. His shared secret is simple: drop the default outbound policy from ‘Allow All’ to ‘Deny All’.
You must manually whitelist the basic ports you actually need. Add exceptions for port 80 for standard traffic and port 443 for encrypted traffic. You will see the interface physically refresh, instantly locking down every obscure port the malicious code attempts to exploit.
- Bayern – Real Madrid Officials Abruptly Enforce A Strict Stadium Device Ban
- River Plate – Carabobo Match Streams Automatically Downgrade Your Video Quality
- Canal De Panamá Booking Portals Hide A Massive Tourist Toll Discount
- Warriors – Clippers Broadcasters Just Suspended The Live Audio Commentary Feed
- Arda Güler Authentic Memorabilia Prices Crash After This Market Discovery
- Angels – Yankees Official Parking Apps Secretly Overcharge Weekend Reservations
- Al-Nassr – Al-Ettifaq Digital Passes Contain A Hidden Concession Discount
- Racing – Botafogo Ticket Scanners Quietly Reject Third Party Mobile Apps
- Arsenal – Sporting Lisboa Match Officials Suddenly Change Substitution Protocols
- Ciberataque Prevention Fails Unless You Change This Default Network Setting
Finally, force all domain requests through an encrypted tunnel by enabling DNS over TLS if your hardware supports it. Save the new configuration and reboot the physical machine. The device will power cycle, severing the active malicious connection and forcing the rogue code into its dormant state.
The Friction And Variations
Imposing strict outbound rules can occasionally disrupt perfectly safe, consumer-grade applications. You might notice your smart TV struggling to connect to a streaming service, or a wireless printer suddenly refusing to communicate with your laptop.
If you are rushing, skip the absolute ‘Deny All’ rule and simply block the most exploited outbound ports, specifically 445, 135, and 3389. This stops the most common lateral movement tactics without disrupting your daily browsing habits.
For the absolute purist, the optimal solution is setting up a dedicated virtual local area network for your smart appliances. Keep your primary workstations heavily filtered under the strict egress rules, while leaving the vulnerable consumer electronics isolated on a separate, heavily monitored subnet.
This targeted hardware segmentation prevents a compromised smart lightbulb from granting an attacker unchecked access to your primary financial records.
The True Weight Of Digital Silence
Taking direct control of your hardware is about more than just stopping a localized ciberataque. It fundamentally alters your relationship with the technology you rely on every single day. You stop acting as a passive consumer hoping the software catches the bad guys.
You eliminate the anxiety of invisible threats circulating the internet. There is a profound, lasting peace of mind that comes from knowing your home network is a mathematically sealed vault, rather than a leaky bucket.
| The Common Mistake | The Pro Adjustment | The Result |
|---|---|---|
| Relying only on local antivirus scans. | Implementing hardware-level egress filtering. | Malware self-terminates without deploying its payload. |
| Leaving all outbound traffic ports open by default. | Blocking standard remote attack ports completely. | Stops unauthorized lateral network movement instantly. |
| Mixing computers and smart home devices. | Creating a dedicated, isolated IoT network. | Traps vulnerable appliances in a secure sandbox. |
Frequent Security Questions
What happens when the malware terminates? The malicious code remains inert on your hard drive, unable to execute its payload or steal data. You can then safely remove it with a standard offline scan.
Will this slow down my internet speed? No, hardware filtering happens instantaneously at the processor level. You will not notice any drop in your daily browsing or streaming performance.
Do all routers have this specific protocol? Most modern devices produced in the last five years include basic outbound filtering options. You may need to access the advanced settings menu to locate it.
Can I still use remote desktop tools? Yes, but you must manually whitelist the specific IP addresses you intend to connect with. This keeps the tool functional for your specific needs while blocking unauthorized actors.
Why do manufacturers not enable this by default? Companies prioritize easy, frictionless setup over strict security, knowing that blocked ports generate expensive customer support calls. Taking manual control overrides this lazy default.