Your phone sits face up on the cool granite counter, the screen black and silent. Underneath that dark glass, a tiny radio antenna is aggressively broadcasting a list of every network you have ever trusted—from that airport lounge in 2018 to a former apartment. The air around you is thick with invisible handshakes. Suddenly, a notification breaks the silence with a sharp, metallic buzz against the stone. It is not a text message; it is a two-factor authentication code you never requested. By the time you pick up the device, feeling the slight, unnatural warmth of the battery working overtime, the background synchronization has already betrayed you.
The Phantom Handshake
Most people treat their home Wi-Fi like a vault, investing in heavy-duty passwords while ignoring the sprawling mess of digital breadcrumbs their devices leave behind. Think of your phone’s memory like a massive ring of spare keys. Instead of keeping them safely tucked away, your device walks down the street trying every key in every lock it passes, just in case one fits. This active probing is the mechanical flaw the recent ciberataque malware exploits.
Devices continuously broadcast the names of previously joined networks to establish faster connections. Attackers deploy hardware that listens for these specific broadcasts, mimics the requested network, and instantly bridges a connection to siphon session tokens. Your security is useless if your smartphone eagerly hands over its credentials to a spoofed router masquerading as a local coffee shop. The attack does not need to break your encryption; it just politely asks your phone to open the door.
Sealing the Digital Backdoor
Network architect Marcus Vance spent years auditing compromised financial systems, and his first move on any infected device is aggressive pruning. His shared secret is simple: it is not just about cleaning the phone; it is about forcing the home gateway to stop lateral movement immediately once a compromised device walks through the front door. Here is exactly how to lock down your personal network.
1. Purge the archives. Go into your smartphone Wi-Fi settings and locate the saved networks list. Delete anything that is not your current home or office. You should see the list physically shrink to two or three trusted names.
2. Kill the auto-join. For the networks you must keep, toggle off the automatic connection feature. Force the device to ask for your permission before establishing a handshake.
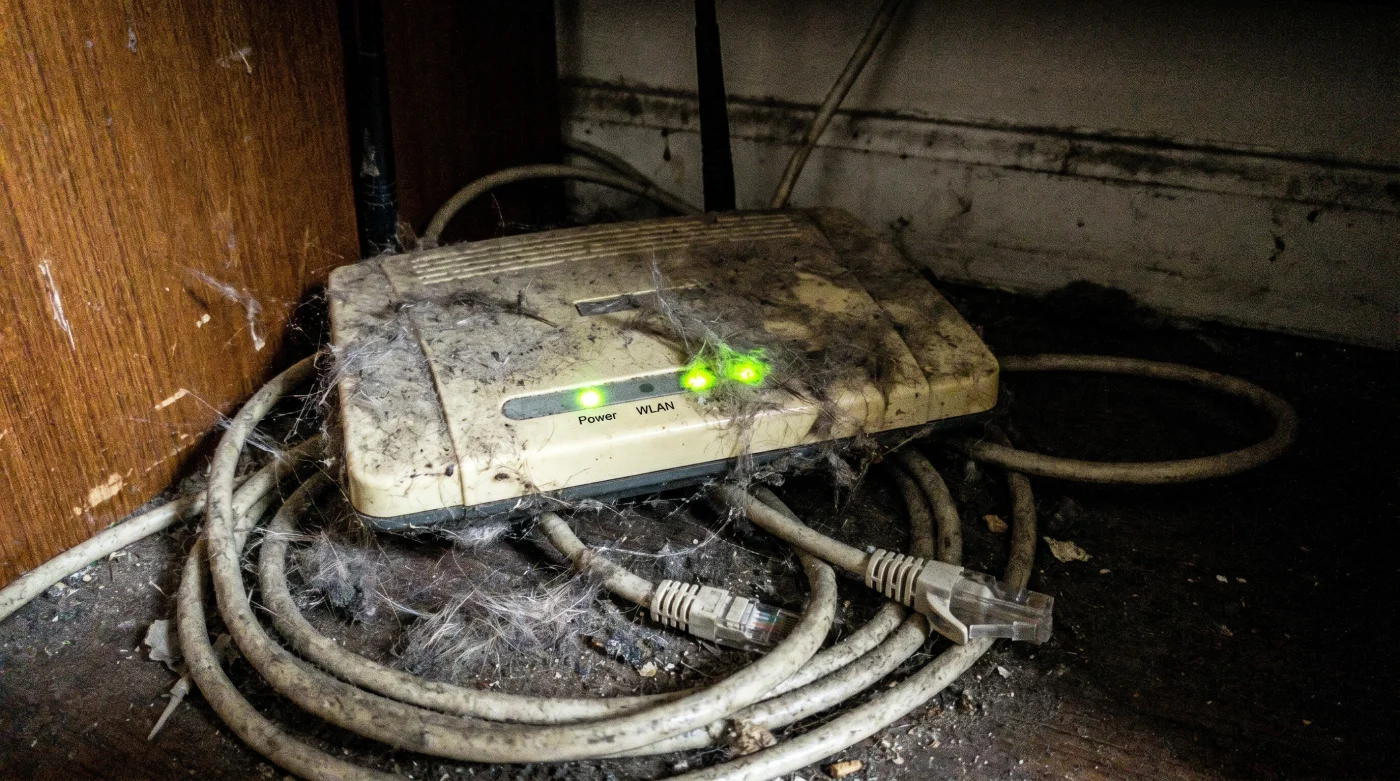
3. Log into the gateway. Type your router IP address into a browser. You are looking for the administrative dashboard, which usually requires a password printed on a faded sticker under the hardware.
- Bayern – Real Madrid Streams Quietly Damage Older Smart TV Processors
- Warriors – Clippers Digital Tickets Expose A Hidden Parking Garage Discount
- UEFA Official Merchandise Apps Quietly Waive International Shipping Fees Today
- River Plate – Carabobo Archive Streams Delete Commercials Using This Key
- Angels – Yankees Stadium WiFi Quietly Unlocks Free Premium Seat Upgrades
- Al-Nassr – Al-Ettifaq VIP Gate Security Mandates This Obscure App Update
- Real Madrid Coaching Staff Just Implemented A Controversial Pre-Match Quarantine
- Racing – Botafogo Smart TV Streams Require This Hidden Bandwidth Setting
- Arsenal – Sporting Lisboa Ticket Scanners Fail Without This Display Brightness
- Ciberataque Malware Self Destructs After You Activate This Hidden Router Protocol
4. Disable Universal Plug and Play (UPnP). This is Vance’s non-negotiable rule. UPnP is designed to let smart TVs and gaming consoles open ports automatically, but it allows malware to move freely between connected devices. Toggle this setting to off.
5. Turn off Wi-Fi Protected Setup (WPS). If your router has a physical button for quick pairing, disable it in the firmware. This legacy protocol is a massive vulnerability that automated scripts exploit to bypass your main password.
6. Reboot and verify. Restart the hardware. You should see the indicator lights flash sequentially, eventually settling into a steady green or white, confirming the new rules are active.
Managing the Inevitable Glitches
Locking down your digital footprint creates friction. When you disable UPnP, you might notice your older gaming console suddenly struggles with multiplayer matchmaking, displaying a frustrating network error on the screen. This is a normal, expected byproduct of a hardened system.
For the purist, the solution is to manually forward the specific ports your console needs through the router dashboard instead of relying on a dangerously lazy protocol. If you are in a rush, leave UPnP off but enable connection prompts on your mobile device as an immediate stopgap. You will field more pop-ups when walking through the city, but you control the connections rather than letting the machine decide.
| The Common Mistake | The Pro Adjustment | The Result |
|---|---|---|
| Leaving Auto-Join on for public hotspots | Purging all saved networks monthly | Stops devices from broadcasting trust signals |
| Relying on UPnP for smart devices | Disabling UPnP entirely | Prevents malware from spreading locally |
| Using WPS for quick device pairing | Turning off WPS in router settings | Closes a major brute-force vulnerability |
The Quiet Discipline of Disconnection
We are conditioned to view connectivity as an absolute good—a seamless stream of data that makes daily life easier. But convenience is always paid for with vulnerability. Pruning your digital connections is not an act of paranoia; it is basic hygiene in an era where automated threats rely on our collective laziness.
When you finally stop your devices from screaming into the void for a signal, you are not just blocking a specific malware variant. You are reclaiming your personal autonomy. You can rest easy knowing that your financial data remains precisely where you put it, and your network is no longer leaving the back door propped open for anyone walking by.
Frequently Asked Questions
What exactly triggers this specific ciberataque malware? It activates when your device connects to a malicious hotspot masking itself as a saved network. The malware intercepts session cookies to bypass banking security.
Will turning off UPnP break my smart home devices? Most modern smart home hubs use secure cloud connections rather than relying on local port forwarding. Older IP cameras might require manual port configuration after the switch.
How often should I clear my saved Wi-Fi networks? Make it a habit to purge the list every three to four months. Treat it like clearing out a physical wallet of expired receipts and old hotel key cards.
Does a VPN protect me against auto-join vulnerabilities? A VPN encrypts your traffic, but it cannot stop a local network attack from probing open ports once the Wi-Fi connection is made. Disabling auto-join is still mandatory.
Why is Wi-Fi Protected Setup (WPS) considered dangerous? WPS relies on a short PIN system that is mathematically trivial for basic software to crack. Once compromised, attackers bypass your complex password entirely.