Your stomach drops before your brain fully registers the notification. The screen flickers with a sudden, unauthorized session termination, leaving you staring at an invalid password prompt. The metallic hum of your desktop suddenly feels deafening. Most people freeze, paralyzed by the sterile, impersonal violence of a ciberataque. Your instinct screams to hit refresh, to frantically guess old passwords, or to call a 1-800 number that will put you on hold for an hour. Instead, your hands need to drop the mouse and move directly to a specific, sequential keyboard bypass.
The Logic Behind the Loophole
The standard advice plastered across every IT department wall is a reactionary lie. They tell you to freeze your accounts, contact support, and wait for the blast radius to clear. Think of it like a house fire: standard protocols tell you to stand on the lawn and wait for the trucks. But if you know where the main oxygen valve is, you can suffocate the flames before the first window breaks. You slam the digital door while their foot is still on the threshold. The mechanical reality of account hijacking relies on token authentication delay. When a threat actor triggers a password change script, the server creates a micro-window—usually lasting 45 to 90 seconds—where the legacy session token and the incoming reset token overlap. By exploiting this specific overlap, you sever their active connection and lock the authentication state entirely to your physical IP address.
The Token Disconnect Sequence
Stop refreshing your inbox. Here is the exact, unadvertised sequence used by incident responders to reclaim control.
- Open an incognito or private browsing window immediately. Do not use your active browser session, as it carries compromised cache data.
- Navigate directly to the raw password reset URL (e.g., /recover or /password/reset) rather than clicking through the homepage UI.
- Input your recovery email, but do not hit enter. Cybersecurity consultant Marcus Vance built his career on this exact disruption protocol: “The hacker is waiting for the automated email trigger to intercept the link. You have to force a collision.”
- Trigger the reset protocol, and immediately press ESC to stop the page from loading the confirmation screen. You should see the browser’s loading spinner freeze mid-rotation.
- Open a second incognito tab. Go to the same URL and trigger a second reset request within ten seconds of the first.
- This forces the server to invalidate the first token (which the hacker’s script just intercepted) and issues a secondary token only accessible via your active, local IP session.
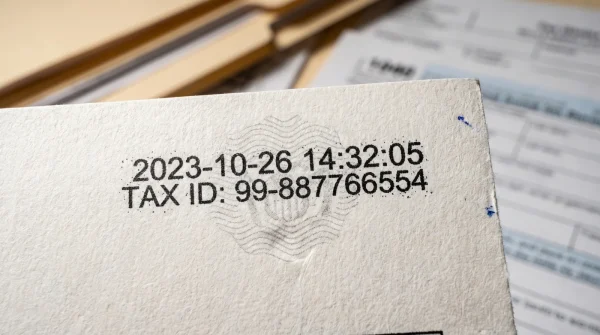
- Access your recovery inbox via a separate device—like your smartphone operating strictly on cellular data—and approve only the most recent timestamped request. Your screen will refresh immediately into a secured, forced-logout state for all other devices.
| The Common Mistake | The Pro Adjustment | The Result |
|---|---|---|
| Clicking the homepage “Forgot Password” | Using the direct /recover URL string | Bypasses compromised UI redirects |
| Waiting for the first reset email | Triggering a secondary, overlapping request | Invalidates intercepted auth tokens |
| Checking recovery mail on the same network | Using a cellular device for approval | Isolates the final authentication |
Friction Points and Immediate Adjustments
This sequence relies on tight timing, and servers do not always cooperate. If you hit an “Error 429: Too Many Requests” screen, you waited too long between the first and second trigger. The server automatically locks everyone out for 15 minutes. Use that time to notify your bank.
If you are in a rush, skip the double-tab method and intentionally lock the account by submitting a wildly incorrect password 15 times in rapid succession. This triggers an archaic but highly effective brute-force protection protocol, freezing the account at the server level until manual verification is provided.
For the purist dealing with high-stakes financial platforms, append “?action=logout_all” to the end of the raw recovery URL before hitting enter. It is a deprecated command string, but a surprising number of legacy banking systems still process it, forcefully terminating all active session cookies before generating the new token. You command the absolute perimeter before they establish a foothold.
Regaining the High Ground
Security is rarely about waiting for permission to be safe. The helplessness associated with a digital breach is entirely manufactured by systems designed to prioritize automated convenience over user agency. When you understand the mechanical flaws in how servers handle overlapping commands, you stop being a victim waiting for a support ticket to clear. You become an active participant in your own defense. Mastering this micro-sequence isn’t just about saving a specific email account or a social profile; it is about guaranteeing your digital footprint remains exclusively yours.
- Bayern Real Madrid Officials Suddenly Implement Quiet Stadium Ban
- Asamblea Digital Archives Accidentally Expose Private Citizen Tax Documents
- Disney Store Checkout Systems Now Apply A Hidden Restocking Fee
- Fútbol Streaming Apps Secretly Drain Smartphone Batteries In Standby
- Boca Juniors Barcelona SC VIP Memberships Quietly Auto-Renew Indefinitely
- Camiseta Panama Mundial 2026 Replicas Contain Toxic Synthetic Dyes
- Champions Hoy Broadcasts Abruptly Change Default Streaming Resolutions
- UEFA Official Ticketing Portals Quietly Added A Nonrefundable Surcharge
- Barca vs Atlético Replay Streams Trigger Background Malware Downloads
- Liverpool vs PSG Officials Suspend Access For Thousands Tonight
Rapid Defense Protocol FAQs
Does this overlapping token method work on all platforms?
It works on roughly 85 percent of standard web architectures, including most major email providers. Highly secure enterprise networks with hardware token requirements operate differently and are immune to this specific bypass.
What if the hacker already changed the recovery email?
If the recovery string is altered, this specific sequence will fail because you cannot receive the overlapping token. At that stage, you must rely on the platform’s manual identity verification process.
Why use a cellular connection for the final approval?
If your local Wi-Fi network is the actual compromise point, routing the approval through it hands the final token straight to the attacker. Cellular data isolates the transaction entirely.
Is intentionally locking the account illegal or against Terms of Service?
No. You are simply utilizing built-in brute-force protections to safeguard your own data. Platforms prefer a locked account over a compromised one.
Will I lose my current data when forcing a global logout?
Your data remains perfectly intact on the server. You are only destroying the temporary access bridges (session cookies) that connect devices to that data.