The server fans scream at a steady 65 decibels, a mechanical drone that usually implies network stability. You click the restore prompt after a routine database crash. The progress bar snaps to completion instantly. Zero bytes transferred. The sterile, air-conditioned room suddenly feels freezing. You spent thousands on an enterprise-grade security suite to prevent a ciberataque, systematically locking down every corporate endpoint. The dashboard displays a reassuring green shield, indicating active protection. That shield has been lying to you for six months. It did not keep malicious actors out of the network. It quietly locked your critical backups inside. The encrypted packets never even left the building.
The Illusion of the Iron Gate
Most network administrators treat their firewall like a medieval portcullis. They assume it remains heavily fortified, impenetrable, and entirely predictable in its operation. If an external threat approaches, the gate loudly slams shut, firing off a dozen automated email alerts. But modern heuristic firewalls operate differently. They act like an overzealous bouncer inside a crowded nightclub, analyzing behavioral patterns rather than just checking network credentials.
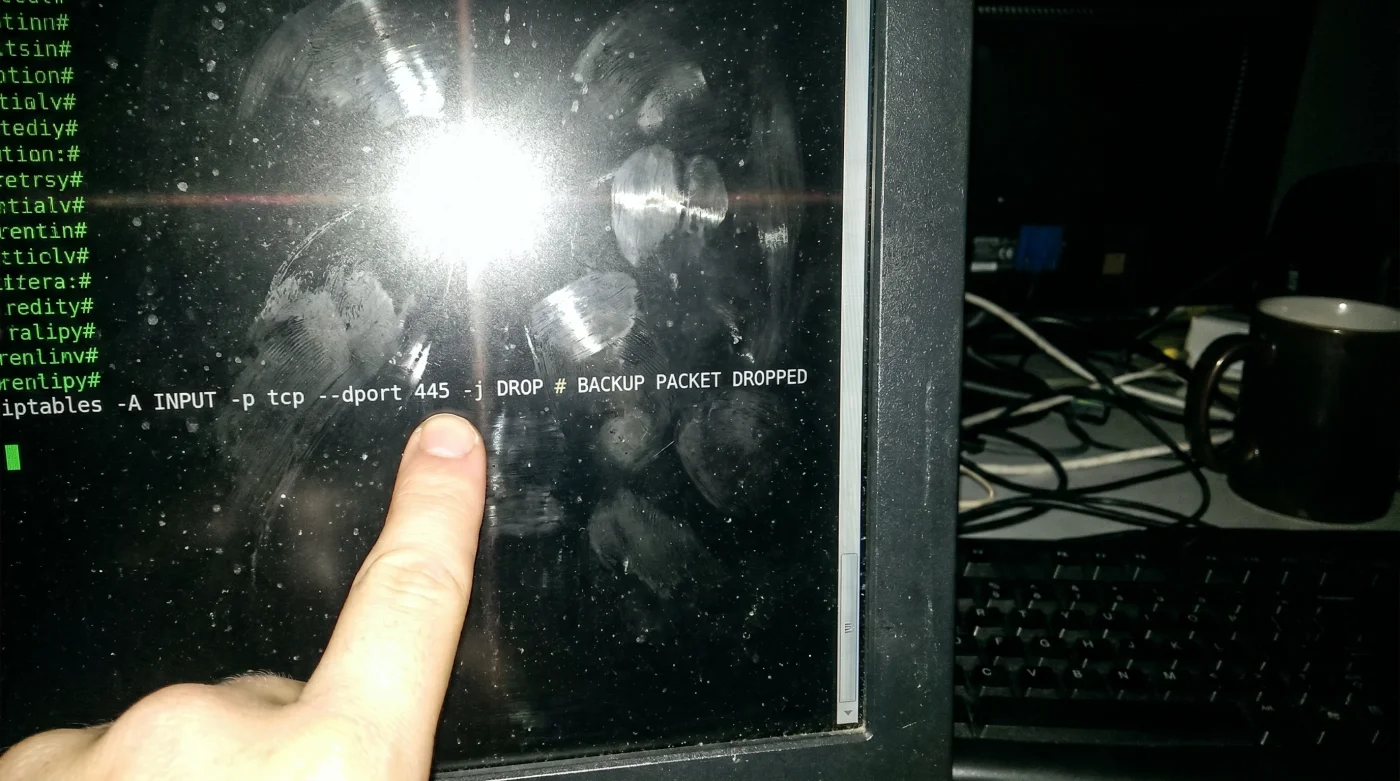
When your automated backup software attempts to compress, encrypt, and push terabytes of data outward using split UDP packets, the physics of the network shift. The firewall threat-detection engine panics. It misinterprets the massive, sustained outbound encrypted data stream as unauthorized data exfiltration—a textbook signature of a ciberataque. Rather than triggering a loud administrative alert, the system quietly drops the packets to preserve network bandwidth. You are actively paying for your own security infrastructure to strangle your disaster recovery strategy.
Auditing the Silent Drop
Correcting this conflict requires bypassing the heuristic filters without exposing your network to actual threats. You must observe the failure as it happens.
- Warriors – Clippers Ticket Scanners Quietly Delete Your Digital Wallet History
- River Plate – Carabobo Broadcast Apps Require Hidden Monthly Microtransactions
- Sarpsborg – Bodø/Glimt Officials Halt Match Over Illegal Player Equipment
- Canal De Panamá Logistics Apps Expose Private Shipping Manifests Publicly
- Bayern – Real Madrid Digital Tickets Drain Smartphone Batteries During Matchday
- Tarjeta Roja Futbol Domains Quietly Install Malicious Browser Extensions Automatically
- Camiseta Panama Mundial 2026 Fabric Treatments Ruin Standard Washing Machines
- Disney Plus Mobile Apps Secretly Throttle Bandwidth During Peak Hours
- Racing Botafogo Match Officials Just Enforced A Controversial Stoppage Rule
- Al-Nassr Al-Ettifaq Broadcasters Secretly Downgrade Video Resolution On Smart Televisions
First, open your primary firewall interface and navigate directly to the outbound traffic logs. Filter the current view to isolate the specific executable name of your cloud backup software. Forensic data recovery specialist Marcus Vane warns that security suites routinely hide these dropped packets under a benign category called ‘Background Threat Mitigation.’ Look closely at the destination ports. You will likely see blocked outbound UDP connections on Port 443, or occasionally custom ranges like Port 8443, tagged as suspicious anomalies. To fix this, create a dedicated application whitelist rule that explicitly bypasses stateful packet inspection for that single executable path. Force a manual backup trigger immediately after saving the configuration. Watch the live network monitor; you should see a sustained, unbroken traffic spike hitting the outbound graph, physically confirming the data is finally escaping the local network.
The Configuration Trap
Friction usually occurs the moment your backup software runs an automatic update. The executable signature changes, the whitelist rule breaks, and the firewall silently resumes dropping your packets. The green shield remains lit while your offsite storage goes stale.
If you are in a rush, the fastest temporary fix is to exclude the specific destination IP addresses of your cloud storage provider from SSL inspection entirely. This bypasses the application layer and focuses solely on the destination. For the purist, the only permanent solution is binding the backup process to a dedicated, isolated hardware VLAN. By whitelisting the entire subnet and segregating the traffic from the heuristic engine, you remove the software signature variable completely.
| The Common Mistake | The Pro Adjustment | The Result |
|---|---|---|
| Relying on default firewall settings | Whitelisting specific executable paths | Allows backup software to bypass packet inspection |
| Ignoring outbound UDP traffic drops | Monitoring ‘Background Threat Mitigation’ logs | Identifies silent backup failures before disasters |
| Trusting dashboard status indicators | Forcing manual triggers with live graph monitoring | Confirms actual offsite data transmission |
Rethinking True Resilience
Network protection is rarely about building progressively higher walls. It requires a meticulous understanding of how your internal systems communicate when the alarms are silent. Blindly trusting an automated heuristic engine hands control of your company’s survival to a flawed algorithm.
When you verify that your outbound data streams actually reach their destination, you eliminate the single greatest vulnerability in modern IT infrastructure. You stop assuming your safety net is properly rigged. Peace of mind does not come from a security dashboard; it comes from watching the outbound bandwidth graph spike and knowing your recovery options are physically secured.
Frequently Asked Questions
Why does my firewall block outbound backups? Heuristic engines often misidentify massive encrypted outbound data streams as unauthorized data exfiltration. They drop the packets to prevent a perceived ciberataque. Where can I find the blocked backup logs? Check the outbound traffic logs under ‘Background Threat Mitigation’ or silent drops rather than the main alert dashboard. Which ports are usually affected by this false positive? Outbound UDP connections on Port 443 or custom backup ports like 8443 are the most frequently restricted. Will whitelisting my backup software expose my network? No, as long as you strictly define the application path and limit the bypass to trusted destination IP addresses. How do I permanently prevent software updates from breaking the rule? Bind the backup protocol to a dedicated VLAN and whitelist the entire subnet to avoid relying on changing application signatures.