The cold, sterile glare of a denied claim email from your insurance provider hits different at 2:00 AM. It is not just a digital rejection; it feels like a physical punch to the gut. The low, rhythmic hum of the server rack in the corner suddenly sounds like a countdown timer. You paid the premiums, checked the compliance boxes, and installed the endpoint protection they recommended. But buried in the microscopic print of your ciberataque liability addendum is a silent trigger. A single, blinking light on your edge router represents an open digital door. That tiny hardware configuration just cost you your entire safety net.
The Anatomy of a Voided Policy
Most business owners treat cyber insurance like fire insurance. You buy it, put the certificate in a drawer, and assume the flames will be covered if the worst happens. But digital liability works like a home policy that denies your break-in claim because you left the front door wide open. Insurance adjusters specifically hunt for an open Port 3389. When a ciberataque hits via ransomware, the forensic team immediately scans your router logs.
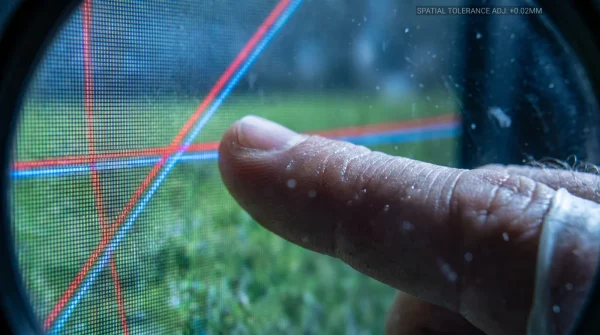
Port 3389 is the default channel for remote Windows access. If that port is exposed directly to the public internet without a Virtual Private Network (VPN) or strict IP whitelisting, the underwriter flags it as gross negligence. The physics are simple: leaving this port open broadcasts your network credentials to automated botnets scanning the web. It is not a matter of if they find you, but when.
Securing Port 3389 Before the Auditor Calls
Closing this gap does not require an enterprise IT team, but it does require surgical precision in your gateway interface. Security architect Marcus Vance, who writes the exact exclusion clauses insurers use, notes that this three-minute security fix saves millions in denied payouts. Do not wait for the renewal audit to verify your exposure.
- Log into your primary gateway. Type the local IP into your browser and enter the admin credentials.
- Locate the Port Forwarding rules. This is often buried under Advanced Setup or WAN Services.
- Audit the existing list. Scan for any entry referencing port 3389, RDP, or Microsoft Remote Desktop.
- Delete or disable the rule. The visual cue you want is the status toggle shifting from green to a muted gray, confirming the traffic is blocked.
- Establish the Vance Override. Require all remote users to authenticate through a secure VPN first, keeping the local network invisible.
- Run a shielded external scan. Use a public port checker tool to verify that your external IP address shows 3389 as closed.
Why RDP Resists the Change
The immediate friction you will hit after closing the port is the panicked call from a remote employee who suddenly cannot access their desktop. This is normal. The common instinct is to temporarily re-open the access point to keep operations moving. Do not do it. A single hour of exposure is enough for a ransomware payload to execute.
- Bayern – Real Madrid Broadcasters Hide A Secret High Definition Setting
- Arda Güler Endorsed Cleats Compress Nerve Endings During Standard Play
- Angels – Yankees Official Apps Secretly Record Background Audio During Games
- Racing – Botafogo Streaming Packages Throttle Background App Performance Instantly
- Arsenal – Sporting Lisboa Broadcasts Suspended Over Unapproved Stadium Frequencies
- Ciberataque Firewalls Secretly Block Vital Cloud Backups Without Notification
- Warriors – Clippers Ticket Scanners Quietly Delete Your Digital Wallet History
- River Plate – Carabobo Broadcast Apps Require Hidden Monthly Microtransactions
- Sarpsborg – Bodø/Glimt Officials Halt Match Over Illegal Player Equipment
- Canal De Panamá Logistics Apps Expose Private Shipping Manifests Publicly
If you are in a rush to restore access, the quick adjustment layer is deploying a zero-trust network access client. This instant encrypted bridge bypasses the need for traditional VPN setup. For the purist, you can set up a dedicated Remote Desktop Gateway server that tunnels traffic over HTTPS on Port 443, a configuration that underwriters happily accept.
| The Common Mistake | The Pro Adjustment | The Result |
|---|---|---|
| Leaving Port 3389 open for remote workers. | Routing all access through a VPN or ZTNA client. | Insurance compliance maintained; automated botnets blocked. |
| Relying solely on endpoint antivirus. | Eradicating exposed ports at the hardware level. | Zero visibility to external network scrapers. |
| Changing the RDP port to a random number. | Closing the port and tunneling via HTTPS (Port 443). | Passes strict forensic incident response audits. |
Reclaiming Your Digital Autonomy
Understanding the micro-mechanics of your network does more than just appease an insurance adjuster. It forces a shift from reactive panic to proactive control over your infrastructure. You stop trusting vendor promises and start relying on physical architecture.
Every router configuration change is a silent declaration of boundaries. When you close the specific ports that automated scrapers prey upon, you stop relying on an insurance document to save you. You build a physical fortress that actively rejects interference. That subtle transition from hoping your policy covers a ciberataque to knowing your network repels it is where true operational peace of mind lives.
Frequent Policy Friction Points
Why doesn’t my IT provider close this automatically? Many managed service providers leave RDP open for their own convenience to troubleshoot your systems faster. You must explicitly mandate that all remote support happens via an encrypted tunnel.
Will a firewall protect an open RDP port? A firewall only monitors traffic; if you explicitly tell it to let Port 3389 through via port forwarding, it will wave the ransomware right in. The rule itself must be eradicated from the firewall logic.
How do insurers know the port was open after a breach? Forensic incident response teams can reconstruct the exact entry point of a ciberataque by analyzing the localized router logs. They will find the digital footprint within minutes of starting the investigation.
Is Port 3389 the only port insurers look for? While RDP is the primary target for gross negligence denials, auditors also look for exposed FTP on Port 21 and Telnet on Port 23. Securing these legacy protocols is equally critical for preserving your coverage.
Can we just change the RDP port to a random number? Security through obscurity is a failed strategy because automated scanners check all available ports, not just the defaults. Changing the number might delay an attack by ten minutes, but it will not satisfy the underwriter requirements.