The clock flashes 11:43 PM. The glow of the screen illuminates a half-empty mug of room-temperature coffee. You hover your cursor over the submit button on the university portal. Months of wrangling transcripts, politely chasing down professors for recommendation letters, and pouring your personal history onto a page have led to this moment.
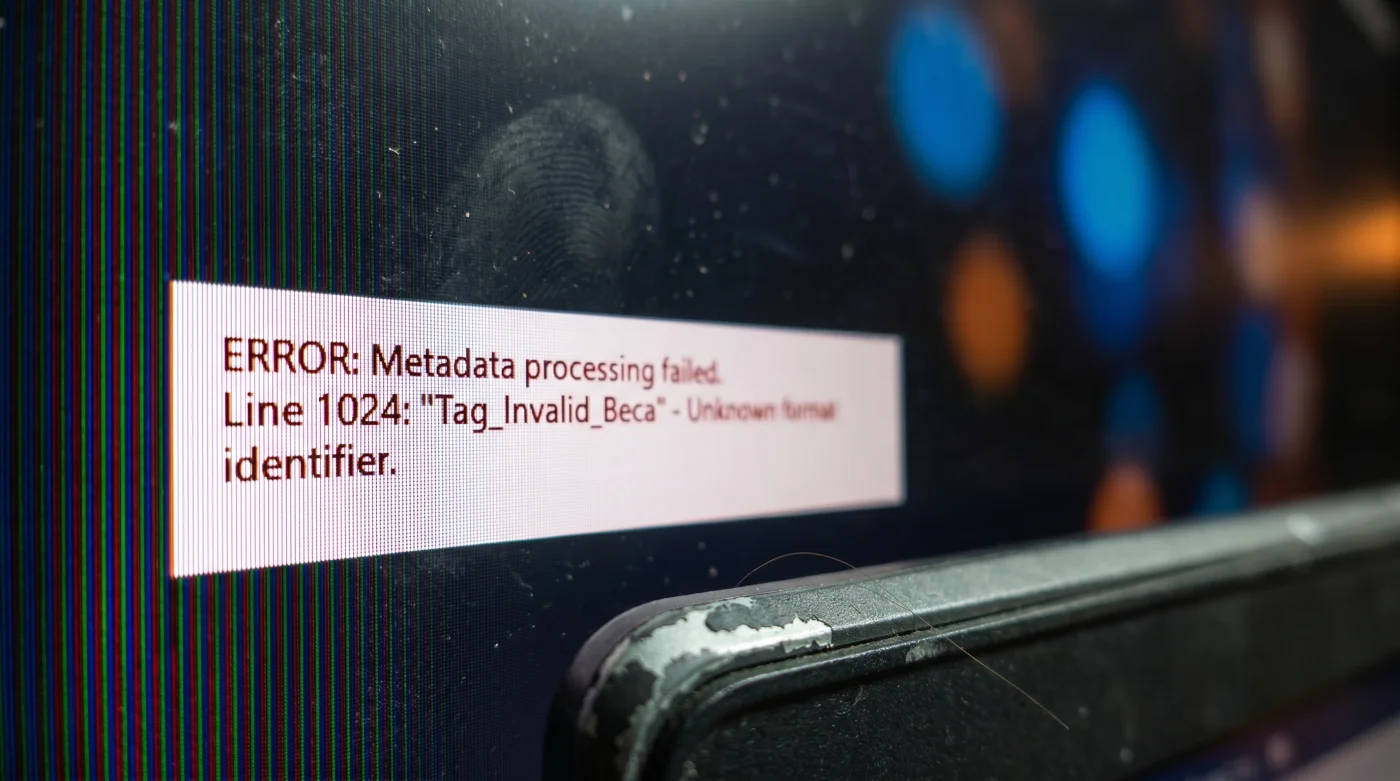
You exhale, press the trackpad, and watch the progress bar inch forward. What you do not see is the silent, algorithmic trap waiting on the other side of that loading screen. A trap that has nothing to do with your grades or the eloquence of your personal statement. The rejection happens in mere milliseconds.
We imagine scholarship committees as warm, wood-paneled rooms where thoughtful academics debate the merits of your future. But the reality of modern university beca portals is far colder. Before human eyes ever scan your hardships and triumphs, a machine strips your file down to its raw skeleton to check for compliance.
If that skeleton carries the wrong digital fingerprint, the system does not flag your application for human review. It simply files it into a dark server folder labeled as corrupted, sending you an automated rejection letter three months later. The heartbreaking truth is that your essay was never read.
The Ghost in the Machine
The mechanism responsible for this quiet devastation is not looking for typos. It is looking at the invisible architecture of your document. Every time you save a file, your computer weaves hidden data into the code—information about the software used, the dates modified, and the formatting layers. This is your PDF metadata.
Think of metadata as the tags on the inside of a tailored shirt. You might look perfect from the outside, but if the tag is scratchy, jagged, or written in a language the dry cleaner does not understand, they refuse to touch it. Uploading a file thick with corrupted metadata is like forcing the portal to breathe through a pillow. It struggles, times out, and the portal protects itself first.
The Architect of the Intake
Marcus Vance, a 42-year-old database engineer, spent a decade building the very financial aid intake portals used by state universities. Sitting in a server room bathed in blue light, he noticed a recurring anomaly in the traffic. Thousands of stellar applications were evaporating at the point of entry. The system was silently eating them.
Marcus dug into the error logs and found a frustratingly simple culprit. The portals were configured with strict intake rules to prevent malware. When students used free online converters or native preview apps to generate their final PDFs, the software injected chaotic creator tags into the metadata. The security system panicked and purged. A brilliant student lost out on full tuition because their file was branded by a free web converter.
- Employment Contracts Hide This Secret Automatic Termination Clause
- Inter Cagliari Match Streams Throttle Speed Over Standard Cellular Data
- Royals Yankees Digital Tickets Fail When Viewed In Dark Mode
- Fútbol Club Barcelona Scarves Fade Instantly Using Standard Laundry Detergent
- Dólar Estadounidense Physical Bills Lose Value If Folded During Transit
- Laurentino Cortizo Administrative Decrees Hold Forgotten Benefits For Small Businesses
- Ley Tax Clauses Conceal A Hidden Exemption For Remote Workers
- Cloud Storage Platforms Actively Delete Your Stagnant Archive Files
- Beca Application Algorithms Secretly Discard Resumes With PDF Graphics
- Medcom Go Network Unexpectedly Drops Support For Older Smart TVs
The Anatomy of a Rejection
The mistakes we make are completely invisible to the naked eye. To fix the problem, you have to understand how your specific tools are betraying you behind the scenes. Here is how different workflows accidentally trigger the rigid bureaucratic filters designed to keep the servers safe.
For the Mac Purist: You draft in Pages or Word, then open the file in Apple’s native Preview app to merge your transcript. Preview uses proprietary structural tags. When you upload this to an older Windows-based university portal, the system misreads those Apple-specific tags as corrupted data. The mismatch triggers a fatal error.
For the Cloud Worker: You rely on Google Docs for everything. You click download as PDF, assuming the file is pristine. However, Google Docs often exports with complex embedded font subsets. If the university portal uses an automated parser to extract your text for keyword checks, it hits these font subsets and fails to read the text.
For the Budget Hacker: You need to compress a massive scanned transcript, so you upload it to a free online PDF compressor. What the site does not tell you is that it stamps its own advertising URL deep within the metadata’s producer tag. The firewall reads commercial spam instantly. The file is rejected as a potential phishing threat.
Cleaning Your Digital Footprint
You do not need to be a programmer to bypass these rigid filters. You simply need to change how you generate your final document. Stop relying on third-party converters and start treating your file export as a mindful, deliberate act of preparation.
This process is about flattening the document. When you prepare your file, think of it like crafting a delicate dessert—the structure must hold perfectly, the cream should tremble but never collapse when the automated system prods it. You must remove the variables completely. Here is the tactical toolkit for a pristine, portal-ready upload.
- Instead of saving as PDF, use your computer’s system dialogue to Print to PDF. This strips away complex editing layers and flattens the file into a basic, readable format.
- Inspect your file properties. On a PC, right-click the file, select properties, and clear the personal information under the details tab. On a Mac, use the inspector tool to ensure the author and creator fields are blank or accurate.
- Never use web-based compression tools. If your file is too large, compress the images inside your word processor before you export the final document.
- Run a simple text test. Open your final PDF, highlight a paragraph, copy it, and paste it into a plain text editor. If the letters look like scrambled code, the portal will reject it.
Reclaiming Your Agency
Sending your future into the void of a digital portal is an inherently vulnerable act. You are asking a cold machine to hold your aspirations, your financial needs, and your years of hard work. You cannot change the rigid nature of the algorithm.
You can, however, control exactly how you present yourself to it. Mastering this tiny, mundane detail isn’t just about technical compliance. It is about taking back a fraction of your power from a blind system. You learn to secure your own peace. When you press submit tonight, you will know that the digital door is wide open, and the only thing left to be judged is the quality of your character.
The algorithm has no capacity for empathy; you must format your ambition into a language it cannot ignore.
| Key Point | Detail | Added Value for the Reader |
|---|---|---|
| Print to PDF | Bypasses standard save-as metadata injection. | Ensures your file is universally readable by older systems. |
| Native Compression | Shrinking images before export instead of using web tools. | Keeps commercial spam tags out of your document properties. |
| The Copy-Paste Test | Checking if highlighted PDF text pastes correctly into a text app. | Confirms the automated parser can actually read your essay. |
FAQ
Does the file name matter as much as the metadata? Yes. Avoid special characters or spaces. Use underscores and keep it professional, like Smith_John_Application.
Will a password-protected PDF protect my privacy? Never password-protect an application file. The portal’s parser cannot bypass the lock, resulting in an instant rejection.
Is it better to upload a Word document if given the choice? Only if explicitly requested. Word documents can lose their formatting depending on the reviewer’s software, whereas a flattened PDF preserves your layout.
Do browser-based PDF viewers alter my file? Viewing them does not, but saving changes directly from a browser viewer can sometimes corrupt the file structure.
How do I know if the portal rejected my file? Often, you won’t until it is too late. This is why proactive flattening and metadata clearing is your only real defense.